Why Quantum Key Distribution?
Security from Physics, Not Mathematics
Classical cryptographic key exchange (Diffie-Hellman, RSA) derives its security from the assumed computational difficulty of mathematical problems — problems that Shor's algorithm would render trivial on a sufficiently powerful quantum computer.
QKD takes a fundamentally different approach. Its security is grounded in the laws of physics: the Heisenberg Uncertainty Principle ensures that measuring a quantum state disturbs it, and the No-Cloning Theorem guarantees that an unknown quantum state cannot be copied. Any eavesdropper who intercepts the quantum channel necessarily introduces detectable errors.
The security of QKD is information-theoretic (sometimes called "unconditional") — it holds against an adversary with unlimited computing power, including future quantum computers.
The BB84 Protocol (1984)
How BB84 Works
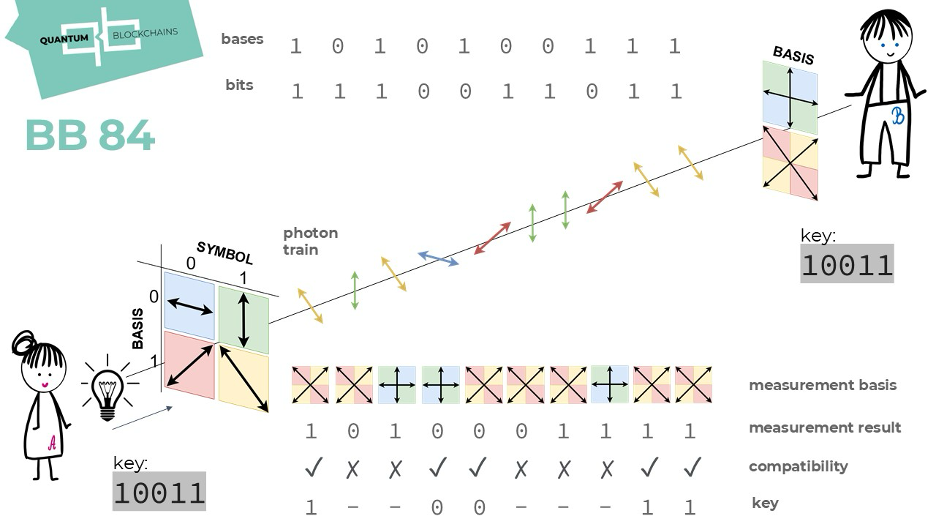
Step 1 — Preparation: Alice randomly selects a bit value (0 or 1) and a basis (rectilinear {|0⟩,|1⟩} or diagonal {|+⟩,|−⟩}) for each qubit she sends to Bob over a quantum channel.
Step 2 — Measurement: Bob independently and randomly chooses a measurement basis for each qubit. When he uses the same basis as Alice, he always measures the correct bit. When the bases differ, his result is random.
Step 3 — Sifting: Alice and Bob publicly announce which bases they used (but not their bit values) via a classical channel. They discard all bits where their bases didn't match — roughly 50%. The remaining bits form the sifted key.
Step 4 — Error estimation: They compare a random sample of their sifted key bits publicly to estimate the Quantum Bit Error Rate (QBER). If QBER exceeds ~11%, the channel is considered compromised and the key is discarded.
Step 5 — Privacy amplification: Classical post-processing (error correction + privacy amplification) distils the remaining bits into a shorter, provably secure final key.
The E91 Protocol (1991)
Entanglement-Based QKD
Approach: Rather than Alice sending prepared qubits, a source distributes pairs of entangled photons — one to Alice, one to Bob. The correlations of their measurements (in randomly chosen bases) produce a shared secret key.
Security mechanism: E91 uses Bell inequality tests to authenticate the quantum channel. Quantum mechanics predicts that entangled measurements violate the CHSH inequality (|S| = 2√2 ≈ 2.83), while any classical or eavesdropped system is bounded by |S| ≤ 2. A deviation from quantum predictions reveals an adversary.
Advantage — Device Independence: In principle, E91's security does not require trusting the hardware, since the Bell test itself certifies quantum behaviour. This makes it the theoretical basis for device-independent QKD.
Protocol Comparison
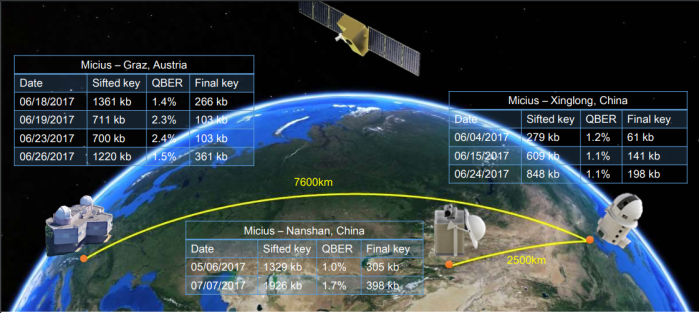
Real-World QKD — Satellite Links
Practical Limitations
Distance Limits
Photon loss in optical fibre (~0.2 dB/km) limits practical QKD range to around 100–200 km without quantum repeaters, which remain an unsolved engineering challenge.
Low Key Rates
Current systems generate keys at kilobits to megabits per second — insufficient for high-throughput applications. AES key exchange is orders of magnitude faster.
Side-Channel Attacks
The protocol may be secure in theory, but hardware implementations can be exploited — e.g. detector blinding attacks manipulate photon detectors. Real-world security requires careful engineering beyond the protocol itself.
Trusted Relay Nodes
Long-distance QKD networks rely on trusted intermediate nodes (e.g. China's 2,000 km Beijing–Shanghai link). Each node is a potential physical vulnerability if compromised.